No final de dezembro de 2025, as infraestruturas energéticas críticas da Polónia — incluindo parques eólicos e solares, centrais de cogeração e sistemas industriais — foram alvo de um ciberataque coordenado, presumivelmente perpetrado por hackers ligados a um Estado-nação.
Eis um resumo rápido do que os atacantes conseguiram:
- Conseguiram o acesso inicial através de dispositivos VPN/firewall expostos (por exemplo, hardware Fortinet), utilizando credenciais predefinidas e sem autenticação multifator
- Uma vez dentro, chegaram ao OT e ao ICS, lançando um malware destrutivo do tipo «wiper», concebido para apagar ou corromper ficheiros nos controladores e nas IHMs
- O ataque provocou a perda de comunicação e monitorização entre as instalações e os operadores da rede, danificou o firmware e chegou mesmo a causar danos permanentes em alguns dispositivos ICS — mas não provocou um apagão.
Como os díodos de dados poderiam ter ajudado
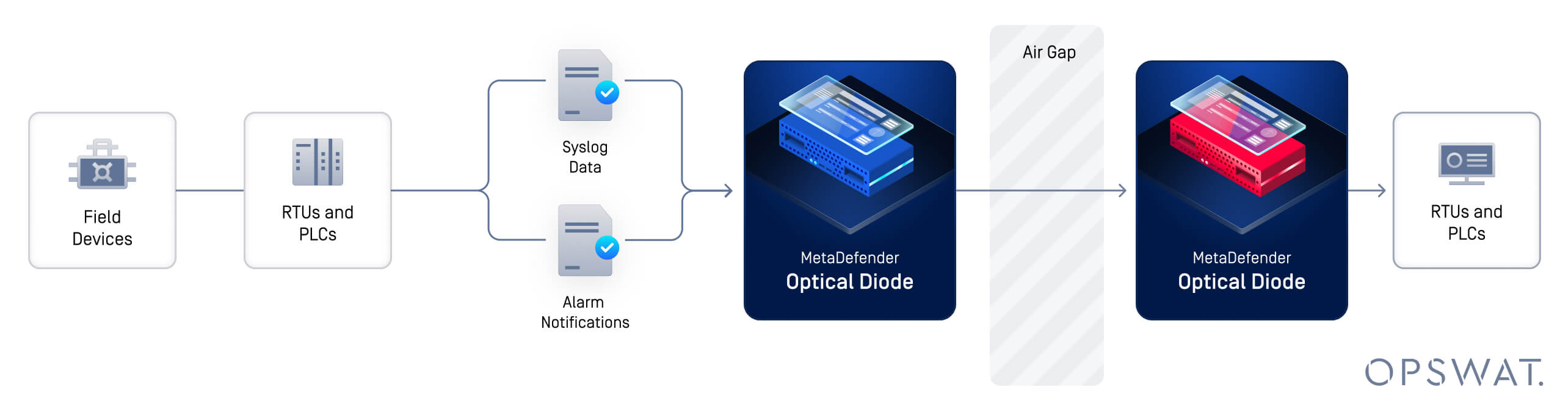
Um diodo de dados é um dispositivo de hardware de cibersegurança que impõe um fluxo de dados unidirecional, o que significa que os dados só podem circular fisicamente numa única direção — de uma rede para outra — sem qualquer possibilidade de tráfego de retorno. Vamos explorar algumas das formas como um diodo de dados poderia ter evitado este ataque.
1. Bloqueio do acesso não autorizado às redes operacionais
Os dispositivos OT e ICS estavam acessíveis através da rede porque o equipamento de perímetro (como gateways VPN) dava acesso a esses ambientes. Os diodos de dados, caso estivessem em uso, poderiam ter sido utilizados entre:
- A rede ligada à Internet e o segmento de TI empresarial
- O segmento de TI empresarial e o domínio OT/ICS
Com um diodo instalado, mesmo que os atacantes comprometessem um serviço VPN, nunca conseguiriam fazer com que o tráfego bidirecional da rede entrasse no domínio OT.
Isto significa que, caso as credenciais fossem roubadas, os atacantes não poderiam enviar comandos ou cargas maliciosas para os sistemas protegidos por um diodo, uma vez que este impede fisicamente que o tráfego entre nessa zona.
2. Proteção dos canais de monitorização/controlo
Alguns sistemas (como painéis de monitorização da rede ou servidores de registos históricos) necessitam frequentemente de dados do ICS, mas nunca precisam de enviar comandos de volta. Com um diodo de dados, os dados OT podem ser enviados para os sistemas de monitorização de forma segura, e nenhum sistema externo ou do domínio da empresa pode iniciar tráfego para os dispositivos OT.
Este é um componente essencial da arquitetura de segurança para ambientes industriais onde o tráfego deve ser unidirecional.
3. Reforço contra movimentos laterais
Neste ataque, uma vez dentro da rede, os atacantes deslocaram-se lateralmente — desde os pontos de entrada até aos domínios Windows de back-end e aos controladores OT. Se houvesse um diodo de dados, a segmentação da rede teria sido fisicamente imposta. Além disso, um diodo teria garantido que as barreiras físicas fossem controladas de forma segura, com fluxos de dados unidirecionais.
Mesmo que um invasor conseguisse entrar num segmento, não conseguiria aceder aos outros segmentos se estes estivessem protegidos por barreiras unidirecionais.
Segurança cibernética em camadas
É importante lembrar que a implementação de diodos de dados é uma parte essencial de uma estratégia global de cibersegurança para as redes operacionais, mas não é a única.
- Implementação de autenticação forte
- Manter-se a par das vulnerabilidades de software ou de configurações incorretas
- Lembre-se de que os díodos são um elemento de controlo no projeto de redes, e não uma ferramenta de monitorização
Por outras palavras, os díodos são mais eficazes quando integrados numa estratégia de defesa em profundidade, que deverá ser combinada com:
- Excelentes credenciais e mestrado em Belas Artes
- Aplicação correta de correções e verificação do firmware
- Segmentação de rede e acesso com privilégios mínimos
- Sistemas de deteção de anomalias e intrusões
Fazer ou Diodo
Os díodos de dados protegem ambientes críticos ao garantir um fluxo de dados unidirecional e fisicamente imposto, tornando muito mais difícil para os atacantes acederem e controlarem os sistemas industriais, mesmo que consigam violar os dispositivos de perímetro. No caso da Polónia — onde os hackers exploraram sistemas expostos à Internet e avançaram lateralmente para o hardware de controlo — a implantação estratégica de díodos poderia ter:
- Caminhos de ataque bloqueados para segmentos OT
- Impediu a execução de comandos maliciosos e a disseminação de malware em sistemas ICS
- Limitou o alcance das ações destrutivas
OPSWATMetaDefender Optical Diode oferece uma variedade de formatos e configurações concebidos especificamente para responder às suas necessidades de proteção do perímetro. Contacte um especialista hoje mesmo e descubra como um dos nossos díodos ou soluções de gateway unidirecional pode manter os seus ambientes críticos seguros.