Avaliação de vulnerabilidades e
s baseadas em ficheiros
Detete vulnerabilidades de software conhecidas através da análise direta de ficheiros, antes mesmo de as aplicações ou bibliotecas serem executadas.File-Based Vulnerability Assessment
File-Based Vulnerability Assessment identificaFile-Based Vulnerability Assessment componentes de software vulneráveis ao nível do ficheiro,
colmatando as lacunas de segurança deixadas pelos tradicionais scanners pós-instalação.
- Detecção pré-instalação
- Perspetiva ao nível binário
- Superfície de ataque reduzida
OPSWAT tem a confiança de
Patenteado
Tecnologia
U.S. 9749349 B1
2.5k
Fornecedores suportados
Mais de 30 mil
CVE associados ao
Informações sobre a gravidade
3M
Hashes vulneráveis identificados no
Analisar
Ficheiros executáveis e instaladores do
Identificar riscos sem depender da pegada do sistema
Analisar o estado de repouso e as aplicações em execução
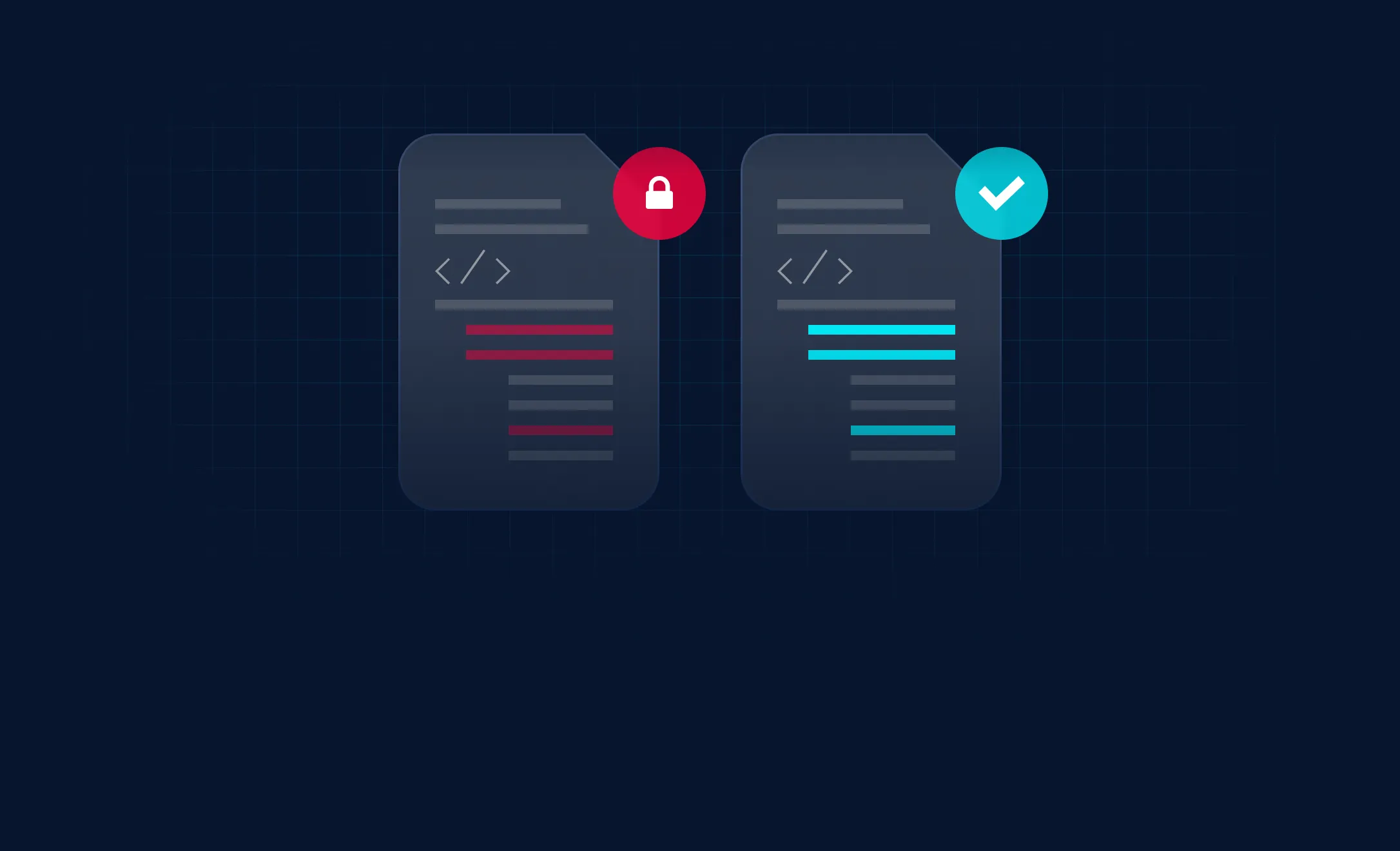
A análise tradicional de vulnerabilidades
deixa lacunas críticas
A análise pós-instalação e a deteção baseada na assinatura não identificam vulnerabilidades no software antes da implementação,
deixando os sistemas expostos a potenciais ameaças.
As vulnerabilidades são detetadas demasiado tarde
A maioria dos scanners só identifica vulnerabilidades depois de o software estar instalado e em funcionamento, criando uma janela de oportunidade em que os atacantes podem explorar pontos fracos conhecidos.

Visibilidade incompleta dos Software
As ferramentas tradicionais dependem de vestígios do sistema, entradas do registo ou gestores de pacotes que podem estar em falta, terem sido alterados ou terem sido ocultados intencionalmente.

Risco elevado em ambientes isolados e de terapia ocupacional
Os ambientes isolados fisicamente, de tecnologia operacional (OT) e de infraestruturas críticas não podem correr o risco de que software vulnerável entre nas redes sem ser detetado através de suportes removíveis ou atualizações.
Vulnerability Detection proativa Vulnerability Detection nível do ficheiro
File-Based Vulnerability Assessment software vulnerável através da análise direta dos ficheiros antes da instalação, execução ou acesso à rede.
Vulnerability Detection do «
» antes da instalação
Analise os ficheiros antes da implementação para identificar vulnerabilidades conhecidas e impedir, desde o início, que software de risco entre nos ambientes.
Software de nível binário
Inteligência
Proteção para ambientes de segurança de alta
Secure sistemas Secure , de tecnologia operacional (OT) e críticos, avaliando os ficheiros antes de estes chegarem às redes isoladas.
Como File-Based Vulnerability Assessment
OPSWAT os ficheiros diretamente e correlaciona-os com vulnerabilidades conhecidas, utilizando inteligência de software avançada.
Características principais
Detecção de vulnerabilidades de tipo «
» antes da execução
Impede a execução de software vulnerável,
reduzindo significativamente a exposição e
eliminando os pontos cegos deixados pela verificação pós-instalação
.
Análise independente da pegada ecológica
Detete vulnerabilidades sem depender de entradas do registo d
, gestores de pacotes ou artefactos de software instalados d
.
Ampla cobertura de formatos de ficheiros
Suporta uma vasta gama de ficheiros binários, incluindo aplicações d
, instaladores e bibliotecas partilhadas.
Implementar em qualquer lugar, integrar em qualquer lugar
Solução escalável e abrangente de segurança de ficheiros que se integra sem problemas e segue os seus ficheiros para onde quer que vão.