OPSWAT protects critical infrastructure, however this is not limited to what governments define as “Critical Infrastructure,” but what you deem critical.
At the center of that infrastructure is critical data – data that ensures safe, stable, and continuous operations.
In ICS (Industrial Control Systems) and OT environments, this data reflects the core functions/processes of the business. But when a cyber incident strikes, one of the first priorities becomes containment.
The Containment Dilemma
The first step in containment is to isolate the affected systems and break connectivity paths that could spread the attack. CISA’s (Cybersecurity and Infrastructure Security Agency) guidance on ransomware response, for example, explicitly calls for immediately isolating impacted systems and disconnecting devices when possible(1). This is sound advice – but in industrial environments it can create an operational dilemma:
| Security Needs Separation | Operations Needs Visibility |
|---|---|
| Stop lateral movement | Are systems still running safely? |
| Stop command-and-control | Are systems stable or trending out of tolerance? |
| Prevent propagation | Do we shut down or can we continue to operate without any incidents? |
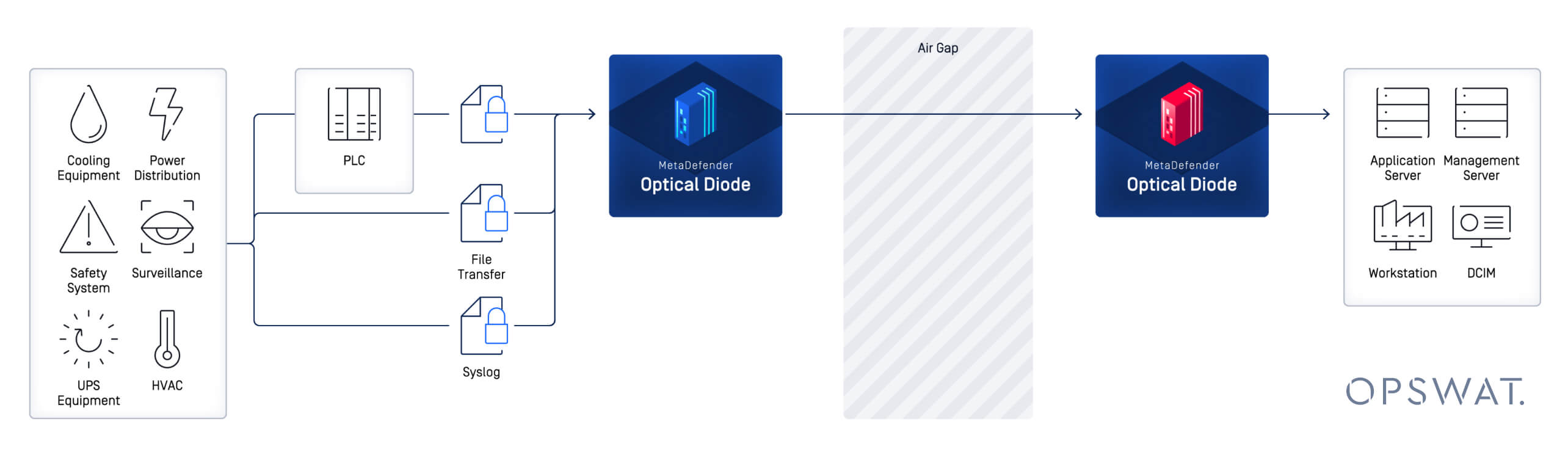
Optical Diodes Remove Any Room for Doubt
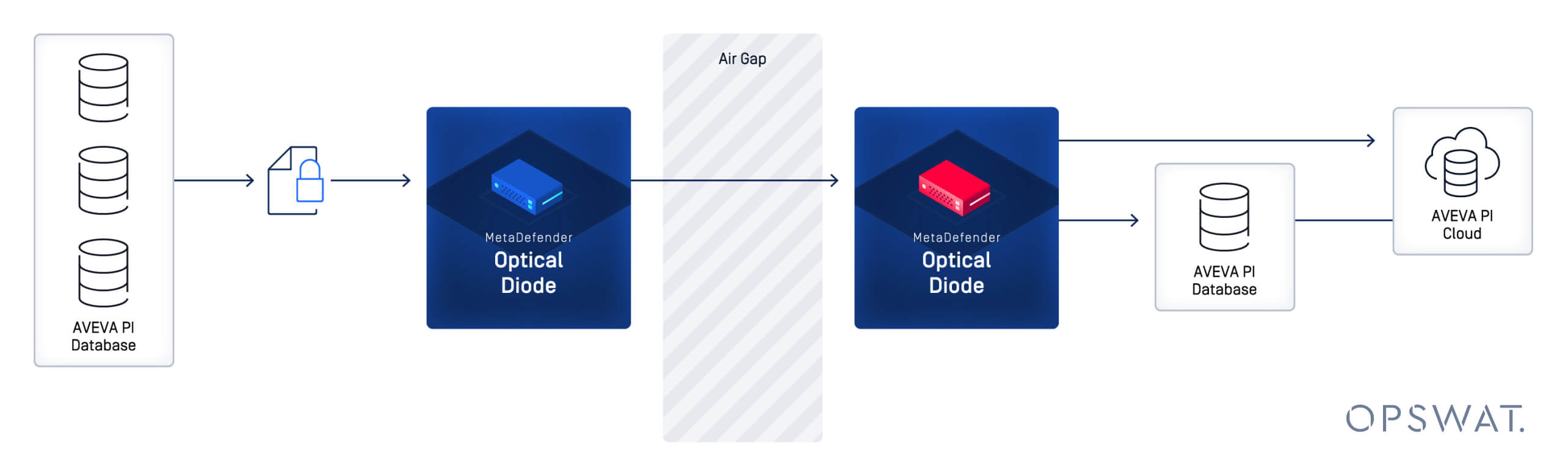
An optical data diode allows organizations to shut down bidirectional pathways, such as firewalls, VPNs, remote access, and trust relationships, while still allowing critical telemetry data to flow outward. This method provides a mechanism for process awareness, improved safety, and better decision-making from real-time data.
The Core Idea
Even though you "close the door" between IT and OT during containment, you can still leave a "mail slot" for read-only process data to egress the OT environment – all without providing a network pathway back in.
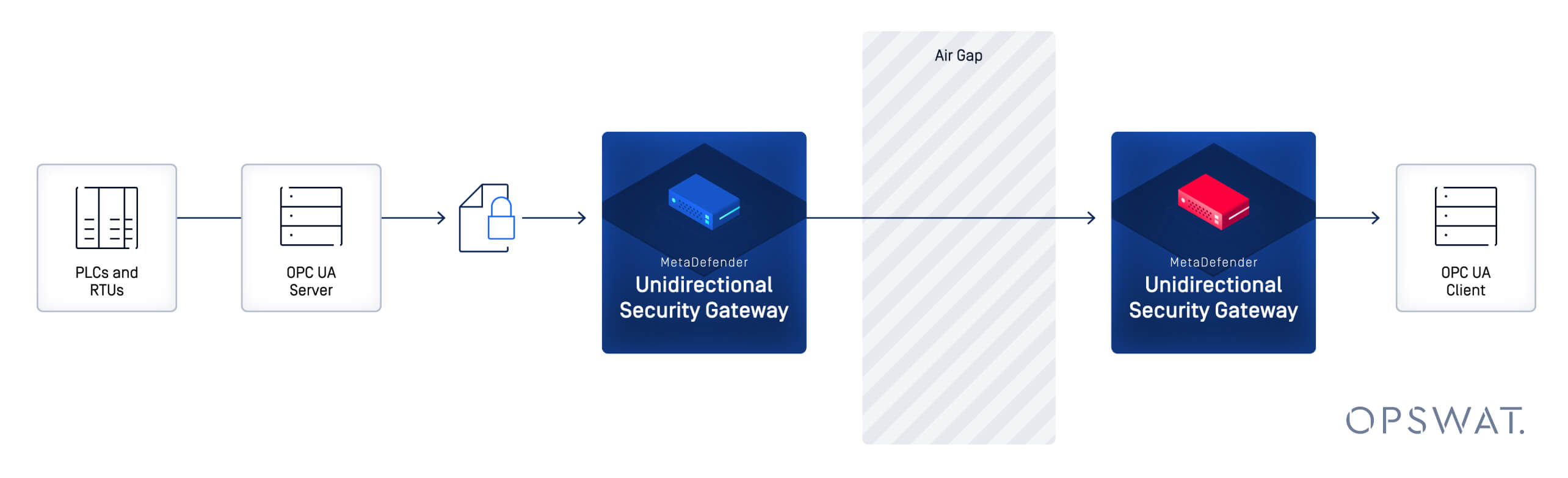
Containment as part of incident response (IR) aligns with longstanding OT security guidance from NIST. NIST notes that an alternative to a firewall is a unidirectional gateway/data diode that permits only authorized, configured communication in one direction(2).
What Happens When Things Go Dark
How do you run manufacturing without automation and infrastructure? A widely cited example of "containment through disconnection" is Norsk Hydro's 2019 ransomware incident, in which the company shut down network access to prevent propagation and fell back to manual processes for a period. The LockerGoga ransomware affected some of their aluminum processing plants the most, and the financial impact would reach upwards of $71 million. Retired plant personnel who understood the old paper system volunteered to return to their plants to keep production going(3).
This case is valuable to understand because it illustrates the operational and financial costs of losing digital connectivity and centralized visibility for automated processes during IR. It was the right call.
Decision Grade Visibility with Containment
In many industrial organizations, process visibility depends on data flowing from OT sources such as:
- OPC UA Servers (real-time values, alarms, contextualized data)
- Historians like AVEVA PI (time-series + events + Asset Framework context)
During containment, it's common to disable firewalls and rules or block remote access to prevent OT telemetry data from connecting to enterprise tools. A diode architecture changes that failure mode:
- You can shut down the firewall/server routes for inbound risk.
- You can still get one-way telemetry data out to maintain situational awareness and faster real-time incident triage.
- If you’re using other visibility tools that rely on network traffic visibility for threat detection, you can keep that data flowing across a diode
Example Scenario
Incident
Ransomware detonates on the corporate network. The incident response team isolates and disables traffic between IT and OT to prevent contamination of the OT infrastructure.
Problem
Central teams lose access to OT dashboards and historian views that provide, “is it safe? Is it stable?” environmental visibility.
With a diode, OT continues streaming read-only telemetry data to a receiver network where SOC/operations leadership can see key trends, alarms, and safety data points – without any control communications back into the OT environment.
While a diode doesn’t “solve ransomware” (look into preventative technologies within MetaDefender Core). It reduces the blast radius by preventing inbound network access from higher-risk zones while preserving a minimum level of operational visibility.
Practical Data to Send
To maintain operational effectiveness, define a Crisis Visibility Dataset in the planning phase of your IR plan. Including data such as:
- Safety-critical Process Values (Pressure, temperature, levels, interlocks)
- Mode/Status indicators (auto/manual, permissive, trips)
- Alarm summaries (counts + top alarms)
- Network health telemetry (critical switches/routers, device/port up/down, Historian health data)
- Minimum Context (asset names/units so teams can interpret quickly)
Referências
1. CISA. https://www.cisa.gov/ransomware-response-checklist; CISA. [Online]
2. NIST . SP800-82r3. NIST. [Online] https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-82r3.pdf.
3. Briggs, Bill. Hackers hit Norsk Hydro with ransomware. The company responded with transparency. Microsoft.com. [Online] 12 16, 2019. https://news.microsoft.com/source/features/digital-transformation/hackers-hit-norsk-hydro-ransomware-company-responded-transparency/.